Troubleshooting and FAQs
Question: What can be done to obtain tamper-proof license locking in the case of virtual machines?
Locking licenses to a computer ID key (hardware key or dongle) provides maximum protection against duplication on a VM. A hardware key cannot be accessed by more than one machine, virtual or real, at any time.
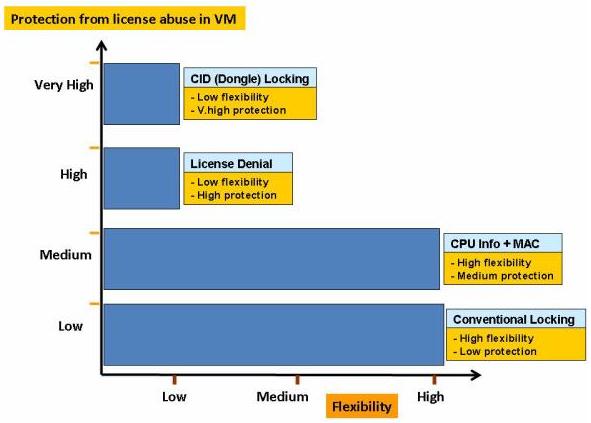
The graph below compares the various locking options on the scale of flexibility versus protection against license abuse:
Question: The strategies provided for tackling misuse of application VMs focus on the License Manager-side. What about providing measures on the client-side?
In the case of network licensing, more threat exists on the License Manager end due to its possible duplication on VMs. Once that risk is reduced through detection and locking mechanisms, the hard limit of a license ensures concurrency and enforcement. Then, whether the clients are real or virtual does not matter.
Question: How do I ensure protection against virtualization in the case of standalone applications?
Since the License Manager is a built-in component in the standalone licensing library, virtual machine detection can still be done. Locking the client licenses to CPU info significantly reduces the risk, as does locking to a computer ID key.
Question: There can be virtualization software beyond the ones listed. In that case, does my virtualization strategy fail?
There could be a scenario when a particular VM is not detected by a Sentinel RMS License Manager. However, you can still use the VM locking piece to prevent the loss caused by hardware duplication.
Question: What will happen when either the client or the License Manager are on different operating systems (like, Linux, Mac, or Solaris)?
The CPU info locking logic and VM detection capability of the License Manager is so far limited to the Windows and Linux systems.
